Integrated Security Solutions for Critical Infrastructure
Discover robust integrated security solutions tailored for critical infrastructure protection against various threats.

Integrated Security Solutions for Critical Infrastructure Protecting Our Lifelines
Understanding Critical Infrastructure Security Challenges
Hey there! Let's talk about something super important but often overlooked: keeping our critical infrastructure safe. We're talking about the stuff that keeps our world running – power grids, water treatment plants, transportation networks, communication systems, and even our financial institutions. These aren't just buildings or networks; they're the lifelines of our society. And honestly, protecting them is a massive undertaking, facing a whole host of challenges that are constantly evolving.
First off, the sheer scale of critical infrastructure is mind-boggling. Imagine trying to secure thousands of miles of pipelines, countless power substations, or sprawling airport complexes. It's not like securing a single office building. These assets are often geographically dispersed, making physical surveillance and access control a logistical nightmare. Plus, many of these facilities are quite old, built long before modern security threats were even a twinkle in a hacker's eye. This means they might have outdated systems, legacy equipment, and a patchwork of security measures that aren't always integrated.
Then there's the threat landscape, which is getting scarier by the day. We're not just worried about physical intruders anymore. Cyberattacks are a huge concern, with nation-states and sophisticated criminal groups constantly trying to breach industrial control systems (ICS) and supervisory control and data acquisition (SCADA) systems. A successful cyberattack on a power grid, for example, could plunge entire regions into darkness, causing widespread chaos and economic damage. And let's not forget about insider threats – disgruntled employees or contractors who might intentionally or unintentionally compromise security. Natural disasters, terrorism, and even simple human error also pose significant risks.
Another big challenge is the convergence of IT (Information Technology) and OT (Operational Technology). Historically, these two worlds were separate, with OT systems managing physical processes and IT systems handling data. But now, they're increasingly interconnected, which brings efficiency but also opens up new vulnerabilities. A cyberattack on an IT network could potentially cascade into the OT environment, disrupting critical operations. Managing this convergence securely requires a deep understanding of both domains and a holistic approach to security.
Finally, regulatory compliance is a constant headache. Governments and industry bodies are always updating security standards and mandates, like NERC CIP for the energy sector or TSA regulations for transportation. Staying compliant isn't just about avoiding fines; it's about ensuring a baseline level of security. But interpreting and implementing these regulations across complex infrastructure can be incredibly challenging and resource-intensive.
So, yeah, critical infrastructure security isn't for the faint of heart. It demands a multi-layered, integrated approach that can adapt to new threats and technologies. That's exactly what we're going to dive into next.
Key Components of Integrated Security for Critical Infrastructure
Alright, so we've established that securing critical infrastructure is a beast of a job. You can't just slap a few cameras up and call it a day. What you need is an integrated security solution – a fancy way of saying all your security systems talk to each other and work together seamlessly. Think of it like a symphony orchestra, where every instrument plays its part in harmony to create something powerful and effective. Let's break down the key components that make up this security symphony.
Physical Security Measures Access Control and Perimeter Protection
This is your first line of defense, the stuff that keeps bad guys out physically. We're talking about robust perimeter fencing, reinforced gates, and bollards to prevent vehicle attacks. But it's not just about barriers; it's about smart barriers. High-definition surveillance cameras, often with advanced analytics like facial recognition or license plate recognition, are crucial. These aren't your grandma's security cameras; they can detect unusual activity, track movement, and even alert security personnel to potential threats before they escalate. Think about thermal cameras for detecting intruders in low light or radar systems for wide-area detection. For access control, we're moving beyond simple key cards. Biometric systems (fingerprint, iris, facial recognition) are becoming more common, especially for highly sensitive areas. Multi-factor authentication, combining something you know (a PIN), something you have (a card), and something you are (a biometric), adds another layer of protection. And don't forget about visitor management systems that track who's coming and going, and for how long.
Cybersecurity Defenses Protecting Digital Assets and SCADA Systems
This is where the IT and OT convergence really comes into play. Protecting critical infrastructure from cyberattacks is paramount. This involves a whole suite of tools and strategies. We're talking about robust firewalls and intrusion detection/prevention systems (IDS/IPS) to block malicious traffic. Endpoint detection and response (EDR) solutions monitor individual devices for suspicious activity. Security information and event management (SIEM) systems collect and analyze security logs from across the entire network, helping security teams spot patterns and respond to threats quickly. For OT environments, specialized industrial cybersecurity solutions are essential. These systems understand the unique protocols and vulnerabilities of SCADA and ICS systems, providing deep packet inspection and anomaly detection to prevent attacks that could disrupt physical operations. Regular vulnerability assessments and penetration testing are also crucial to identify and fix weaknesses before attackers can exploit them. And, of course, strong encryption for data in transit and at rest is a must.
Operational Technology OT Security and Industrial Control Systems
This deserves its own spotlight because OT security is distinct from traditional IT security. While IT focuses on data confidentiality, integrity, and availability, OT prioritizes availability and safety above all else. A cyberattack that takes down a power plant's control system isn't just a data breach; it's a potential catastrophe. OT security involves segmenting networks to isolate critical systems, implementing strict access controls for OT devices, and using specialized security tools designed for industrial environments. This includes things like protocol whitelisting, which only allows approved communications, and continuous monitoring of OT networks for any deviations from normal behavior. Patch management for OT systems can be tricky due to uptime requirements, so robust change management processes are vital. Training for OT personnel on cybersecurity best practices is also incredibly important, as human error can often be a weak link.
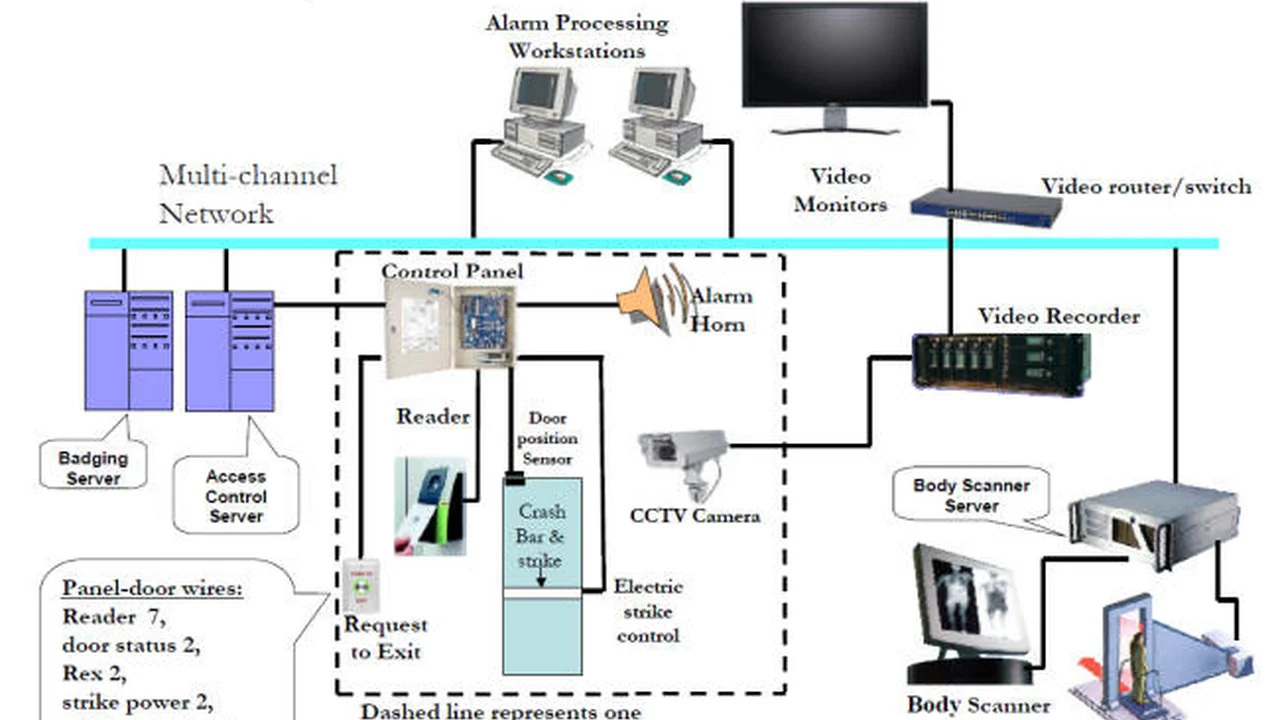
Integrated Command and Control Centers Centralized Monitoring and Response
This is the brain of your integrated security solution. Imagine a room with giant screens displaying real-time feeds from hundreds of cameras, sensor data, access control events, and cybersecurity alerts. A well-designed command and control center (often powered by a Physical Security Information Management, or PSIM, system) brings all this information together into a single, unified view. This allows security operators to quickly assess situations, correlate events from different systems, and coordinate a rapid response. For example, if a perimeter sensor detects an intrusion, the system can automatically pull up camera feeds from that area, lock down nearby access points, and alert the nearest security patrol. This centralized approach drastically reduces response times and improves situational awareness, which is absolutely critical when every second counts.
Intelligent Surveillance and Analytics AI Powered Detection
Gone are the days of security guards staring at dozens of monitors, hoping to spot something. Modern surveillance is intelligent. AI-powered video analytics can do things like detect abandoned objects, identify loitering, count people, recognize faces (with proper privacy considerations, of course), and even analyze crowd behavior. For critical infrastructure, this means fewer false alarms and more accurate threat detection. Imagine an AI system that can distinguish between a bird flying past a fence and a human attempting to climb it. Or an analytics platform that can detect unusual patterns in network traffic that might indicate a cyberattack in progress. These systems learn over time, becoming more effective at identifying genuine threats and reducing the burden on human operators. They can also integrate with other systems, triggering alerts or actions based on what they detect.
When all these components work together, you get a truly robust and resilient security posture. It's about creating layers of defense, both physical and digital, that are constantly communicating and adapting to protect our most vital assets.
Top Integrated Security Solutions for Critical Infrastructure Product Recommendations and Comparisons
Okay, so we know what goes into an integrated security solution for critical infrastructure. Now, let's get down to some specifics. What are some of the leading platforms and products out there that can help achieve this level of protection? This isn't an exhaustive list, but it covers some of the big players and their strengths, along with a rough idea of pricing and typical use cases. Keep in mind, these are enterprise-grade solutions, so pricing is usually custom-quoted based on the scale and complexity of the deployment.
Genetec Security Center Unified Security Platform
What it is: Genetec Security Center is a powerhouse. It's not just a video management system (VMS) or an access control system (ACS); it's a truly unified platform that brings together video surveillance, access control, automatic license plate recognition (ALPR), and communications management into a single interface. This means all your security data is in one place, making it incredibly easy for operators to monitor and respond to incidents.
Key Features for Critical Infrastructure:
- Unified Architecture: Seamlessly integrates all security components.
- Scalability: Designed to handle massive deployments, perfect for sprawling infrastructure.
- Cybersecurity Focus: Built with cybersecurity best practices in mind, offering robust encryption and authentication.
- Advanced Analytics: Offers a wide range of video analytics, including object detection, intrusion detection, and forensic search.
- Federation: Allows multiple independent Security Center systems to be linked, ideal for organizations with geographically dispersed sites.
- Open Platform: Integrates with a vast ecosystem of third-party hardware and software.
Typical Use Cases: Airports, seaports, large utility companies (power, water), government facilities, large industrial complexes.
Pricing: Enterprise-level, custom quotes. Expect significant investment, often starting in the tens of thousands for smaller deployments and easily reaching hundreds of thousands or millions for large-scale critical infrastructure projects. It's a premium solution for premium protection.
Comparison Point: Often compared to other unified platforms like Johnson Controls C•CURE 9000 or LenelS2 OnGuard, but Genetec is often lauded for its truly unified architecture from the ground up, rather than being an integration of separate systems.
Honeywell Enterprise Buildings Integrator EBI
What it is: Honeywell EBI is more than just security; it's a comprehensive building management system that integrates security, fire safety, access control, and building automation (HVAC, lighting, etc.) into a single platform. For critical infrastructure, this holistic view is incredibly valuable, as operational efficiency and safety are just as important as security.
Key Features for Critical Infrastructure:
- Holistic Building Management: Integrates security with operational systems.
- Advanced Event Management: Sophisticated alarm management and workflow automation.
- Scalability and Redundancy: Designed for high availability and resilience, crucial for critical operations.
- Cybersecurity: Strong focus on protecting both IT and OT components.
- Compliance Reporting: Helps meet regulatory requirements with detailed audit trails.
Typical Use Cases: Power plants, refineries, large manufacturing facilities, data centers, airports where operational control is tightly linked with security.
Pricing: Similar to Genetec, EBI is an enterprise solution with custom pricing. It's a significant investment, reflecting its comprehensive capabilities across multiple building systems.
Comparison Point: While Genetec focuses purely on security unification, Honeywell EBI extends that unification to broader building and operational management, making it a strong contender where convergence of security and operations is key.
Siemens Siveillance Suite
What it is: Siemens, a global industrial giant, offers the Siveillance Suite, a robust portfolio of security solutions including Siveillance VMS (video management), Siveillance Access (access control), and Siveillance Control (PSIM). These components can be deployed individually or as a fully integrated suite, providing flexibility for different critical infrastructure needs.
Key Features for Critical Infrastructure:
- Modular and Scalable: Allows organizations to build out their security system as needed.
- High Reliability: Backed by Siemens' industrial-grade engineering and support.
- Advanced Video Analytics: Includes intelligent video analytics for proactive threat detection.
- Integration Capabilities: Strong integration with other Siemens industrial automation and building technologies.
- Cybersecurity: Designed with a focus on protecting critical systems from cyber threats.
Typical Use Cases: Transportation hubs, energy facilities, industrial plants, government buildings, large corporate campuses.
Pricing: Enterprise-level, custom quotes. Expect pricing in line with other major players like Genetec and Honeywell, depending on the modules and scale of deployment.
Comparison Point: Siemens Siveillance often stands out due to its deep integration potential with other Siemens industrial and building automation products, offering a truly comprehensive solution for organizations already using Siemens technology.
Johnson Controls C•CURE 9000 Access Control and Security Management
What it is: C•CURE 9000 is a highly regarded access control and event management system from Johnson Controls (formerly Software House). While primarily an access control platform, it offers extensive integration capabilities with video surveillance, intrusion detection, and other security systems, effectively acting as a PSIM for many organizations.
Key Features for Critical Infrastructure:
- Robust Access Control: Industry-leading access control features, including advanced credential management and policy enforcement.
- Powerful Event Management: Sophisticated alarm monitoring, event correlation, and customizable workflows.
- Extensive Integrations: Integrates with a wide array of third-party VMS, intrusion panels, and other security devices.
- Scalability: Capable of managing thousands of readers and millions of cardholders across multiple sites.
- High Availability: Designed for continuous operation with redundancy options.
Typical Use Cases: Data centers, government facilities, large corporate headquarters, airports, pharmaceutical plants, any facility with complex access control needs.
Pricing: Enterprise-level, custom quotes. Pricing will vary significantly based on the number of readers, integrations, and features required. It's a premium access control solution.
Comparison Point: C•CURE 9000 is often seen as a benchmark for enterprise access control. While it integrates well with video, its core strength is access management, whereas Genetec is more natively unified across video and access.
Palo Alto Networks Industrial Control System Security
What it is: While not a physical security platform, Palo Alto Networks is a leader in cybersecurity, and their solutions are absolutely critical for protecting the OT side of critical infrastructure. They offer next-generation firewalls, threat intelligence, and specialized solutions for ICS/SCADA environments.
Key Features for Critical Infrastructure:
- Next-Generation Firewalls: Deep packet inspection and application-level control for both IT and OT networks.
- Threat Prevention: Advanced malware prevention, exploit prevention, and URL filtering.
- OT Visibility and Control: Specialized capabilities to identify and secure industrial protocols and devices.
- Threat Intelligence: Real-time threat intelligence updates to protect against emerging threats.
- Network Segmentation: Crucial for isolating critical OT systems from broader IT networks.
Typical Use Cases: Any critical infrastructure organization with interconnected IT/OT networks, including power grids, water utilities, manufacturing, and transportation.
Pricing: Varies widely based on the size of the network, number of firewalls, and subscription services. Can range from thousands to hundreds of thousands annually for large deployments.
Comparison Point: This isn't a direct competitor to the physical security platforms but rather a complementary and essential component. You'd typically deploy Palo Alto Networks alongside a Genetec or Honeywell system to cover the cyber aspect.
Choosing the right solution involves a deep dive into your specific needs, existing infrastructure, budget, and regulatory requirements. It's rarely a one-size-fits-all situation, and often involves a combination of these types of solutions working together.
Designing an Effective Integrated Security System for Critical Infrastructure Best Practices
So, you've got a handle on the challenges and the cool tech available. But how do you actually put it all together to create a security system that truly works for critical infrastructure? It's not just about buying the most expensive gear; it's about smart planning and execution. Here are some best practices to keep in mind when designing an effective integrated security system.
Conduct a Thorough Risk Assessment and Threat Modeling
Before you even think about buying a single camera or access card reader, you need to understand what you're protecting and what you're protecting it from. A comprehensive risk assessment is your starting point. This means identifying all your critical assets – physical, digital, and human. What are the crown jewels? What would cause the most damage if compromised? Then, you need to identify potential threats: cyberattacks, physical intrusions, insider threats, natural disasters, terrorism, and even accidental damage. For each threat, assess its likelihood and potential impact. Threat modeling takes this a step further, actively thinking like an attacker to identify vulnerabilities in your current systems and processes. This exercise helps you prioritize your security investments and focus on the most significant risks. Don't skip this step; it's the foundation of everything else.
Adopt a Layered Security Approach Defense in Depth
Think of security like an onion, with multiple layers of protection. If an attacker breaches one layer, they hit another, and another. This concept is called 'defense in depth.' For critical infrastructure, this means combining physical security (fences, guards, cameras) with electronic security (access control, intrusion detection) and cybersecurity (firewalls, IDS/IPS, encryption). It also means having redundant systems, backup power, and diverse communication paths. For example, a perimeter fence might be the first layer, followed by video analytics detecting an intruder, then an access control system preventing entry to a building, and finally, an internal network segmentation preventing a cyberattack from reaching critical control systems. Each layer should ideally be independent, so a failure in one doesn't compromise the others.
Prioritize OT Security and IT OT Convergence
We've talked about this, but it's so important it bears repeating. OT security is not IT security. While there are overlaps, the priorities and technologies are different. When designing your integrated system, ensure that OT security is given its own dedicated focus. This means implementing specialized firewalls for industrial networks, using secure protocols, and segmenting your OT network from your IT network as much as possible. Any points of convergence between IT and OT must be heavily secured and monitored. This might involve using data diodes for one-way communication or highly controlled gateways. Training for both IT and OT teams on the unique aspects of converged security is also crucial to bridge the knowledge gap.
Ensure Scalability and Future Proofing
Critical infrastructure is constantly evolving, and so are threats. Your security system needs to be able to grow and adapt. Choose platforms and technologies that are scalable, meaning they can easily accommodate new cameras, sensors, access points, or network devices without a complete overhaul. Look for open architectures and APIs that allow for integration with future technologies. Investing in proprietary systems that lock you into a single vendor can be a costly mistake down the line. Think about how new technologies like drones for surveillance, advanced AI, or even quantum-resistant cryptography might fit into your security roadmap in the future.
Implement Robust Incident Response and Disaster Recovery Plans
No security system is 100% foolproof. Incidents will happen. The key is how quickly and effectively you can detect, respond to, and recover from them. An integrated security system should feed into a well-defined incident response plan. This plan should outline roles and responsibilities, communication protocols, and step-by-step procedures for various types of incidents (e.g., physical breach, cyberattack, natural disaster). Regular drills and tabletop exercises are essential to test these plans and ensure everyone knows what to do under pressure. Disaster recovery plans are equally important, ensuring that critical operations can be restored quickly after a major disruption, whether it's a cyberattack or a flood. This includes data backups, redundant systems, and alternative operational procedures.
Regular Audits Maintenance and Training
A security system isn't a set-it-and-forget-it solution. It requires continuous attention. Regular audits of your security posture, both internal and external, are vital to identify weaknesses and ensure compliance. This includes penetration testing for cybersecurity and physical security assessments. Maintenance is also key – ensuring all cameras are working, sensors are calibrated, and software is updated. And finally, training. Your security personnel are your most valuable asset. They need ongoing training on new threats, system functionalities, and incident response procedures. A sophisticated system is only as good as the people operating it. Regular refreshers and scenario-based training can make a huge difference in their effectiveness.
By following these best practices, critical infrastructure organizations can build integrated security systems that are not only robust and resilient but also adaptable to the ever-changing threat landscape. It's a continuous journey, but one that's absolutely essential for protecting our collective future.
The Future of Integrated Security for Critical Infrastructure Emerging Trends
Alright, so we've covered the current state of play, but what's next? The world of security, especially for something as vital as critical infrastructure, is always evolving. New threats emerge, and new technologies pop up to counter them. Let's peek into the crystal ball and see some of the exciting and sometimes a little scary trends shaping the future of integrated security for critical infrastructure.
Artificial Intelligence and Machine Learning for Predictive Security
AI and ML are already making waves, but their role is only going to get bigger. We're moving beyond just detecting anomalies to predicting them. Imagine a system that analyzes vast amounts of data – video feeds, sensor data, network traffic, weather patterns, social media sentiment – and can identify subtle indicators that suggest a potential threat is brewing. For example, AI could predict a potential physical intrusion based on unusual vehicle patterns combined with chatter on dark web forums. On the cybersecurity front, ML algorithms are becoming incredibly adept at identifying zero-day exploits and sophisticated malware that traditional signature-based systems might miss. The goal is to move from reactive security to proactive, even predictive, security, giving operators more time to intervene before an incident occurs. This also means fewer false positives, making security teams more efficient.
Blockchain for Enhanced Data Integrity and Trust
Blockchain isn't just for cryptocurrencies anymore. Its core principle of a distributed, immutable ledger has huge implications for security, especially in critical infrastructure where data integrity is paramount. Imagine using blockchain to secure access control logs, ensuring that no one can tamper with who entered or exited a facility. Or using it to verify the integrity of firmware updates for OT devices, preventing malicious code injection. Blockchain could also be used for secure identity management, ensuring that only authorized personnel and devices can access critical systems. While still in its early stages for physical security, the potential for creating highly trustworthy and tamper-proof security records is immense.
Quantum Computing and Post Quantum Cryptography
This one's a bit further out, but it's a game-changer. Quantum computers, once they become powerful enough, will be able to break many of the encryption algorithms we rely on today, including those protecting critical infrastructure data. This is a huge concern for long-term data security. The good news is that researchers are already working on 'post-quantum cryptography' – new encryption methods designed to be resistant to quantum attacks. Critical infrastructure organizations will need to start planning for this transition, evaluating their current cryptographic infrastructure and understanding how they will migrate to quantum-resistant solutions in the coming years. It's a race against time, but an essential one.
Drones and Robotics for Autonomous Surveillance and Response
Drones are already used for perimeter patrols and inspecting hard-to-reach areas. In the future, we'll see more autonomous drones and ground robots integrated directly into security systems. Imagine a drone automatically deploying to investigate an alarm triggered by a perimeter sensor, providing real-time video feedback to the command center. Or robots patrolling vast industrial sites, equipped with thermal cameras and gas detectors. These autonomous systems can significantly extend the reach and efficiency of security personnel, especially in dangerous or remote environments. Of course, regulatory hurdles and ethical considerations around autonomous response will need to be addressed, but the technology is rapidly advancing.
Hyper-Convergence and Cloud-Native Security Solutions
The trend towards hyper-convergence, where computing, storage, and networking are integrated into a single system, is also impacting security. This can simplify deployment and management of security infrastructure. Furthermore, cloud-native security solutions are gaining traction, offering scalability, flexibility, and often more advanced threat intelligence capabilities. While critical infrastructure often has on-premise requirements for core OT systems, hybrid cloud models, where some security functions are managed in the cloud, are becoming more common. This allows for centralized management of distributed sites and leverages the power of cloud computing for analytics and threat intelligence.
Increased Focus on Human Factors and Security Culture
Even with all the fancy tech, humans remain a critical link in the security chain. Future integrated security solutions will place an even greater emphasis on human factors – how operators interact with systems, how they make decisions under pressure, and how to minimize human error. This includes more intuitive user interfaces, AI-assisted decision-making tools, and advanced training simulations. Beyond that, fostering a strong security culture within the entire organization, from the CEO to the frontline technician, will be paramount. Everyone needs to understand their role in maintaining security, reporting suspicious activity, and adhering to best practices. Because ultimately, the most sophisticated system can be undermined by a single careless act.
The future of critical infrastructure security is about leveraging these advanced technologies to create systems that are not just reactive, but intelligent, predictive, and resilient. It's a complex but incredibly important journey to safeguard the foundations of our modern world.
:max_bytes(150000):strip_icc()/277019-baked-pork-chops-with-cream-of-mushroom-soup-DDMFS-beauty-4x3-BG-7505-5762b731cf30447d9cbbbbbf387beafa.jpg)