Integrated Security Solutions for Government Facilities
Discover highly secure integrated security solutions designed for government facilities meeting stringent compliance.

Discover highly secure integrated security solutions designed for government facilities meeting stringent compliance.
Integrated Security Solutions for Government Facilities
The Unique Security Challenges of Government Facilities
Government facilities, from local municipal buildings to federal agencies and critical infrastructure, face a unique and complex set of security challenges. It's not just about protecting property; it's about safeguarding sensitive information, ensuring the safety of personnel and the public, maintaining operational continuity, and adhering to strict regulatory compliance. These facilities are often high-profile targets for various threats, including terrorism, espionage, cyberattacks, vandalism, and insider threats. The sheer volume of people, both employees and visitors, entering and exiting these premises daily adds another layer of complexity to security management. Furthermore, the diverse nature of government operations, ranging from administrative offices to research labs and public service centers, means that a one-size-fits-all security approach simply won't cut it. Each facility requires a tailored, robust, and adaptable security framework. Traditional, siloed security systems – where access control, video surveillance, and alarm systems operate independently – often create gaps in coverage, lead to inefficient response times, and make it difficult to gain a holistic view of security events. This is where integrated security solutions come into play, offering a unified platform that brings together various security technologies to create a more cohesive, intelligent, and effective defense system. For government facilities, integration isn't just a convenience; it's a necessity for achieving the highest levels of security and compliance.What are Integrated Security Solutions for Government Facilities
Integrated security solutions for government facilities are comprehensive systems that combine multiple security technologies into a single, centrally managed platform. Think of it as a security ecosystem where all components communicate and collaborate seamlessly. This typically includes:- Access Control Systems: Managing who can enter and exit specific areas, at what times, and under what conditions. This can range from traditional card readers to advanced biometric systems.
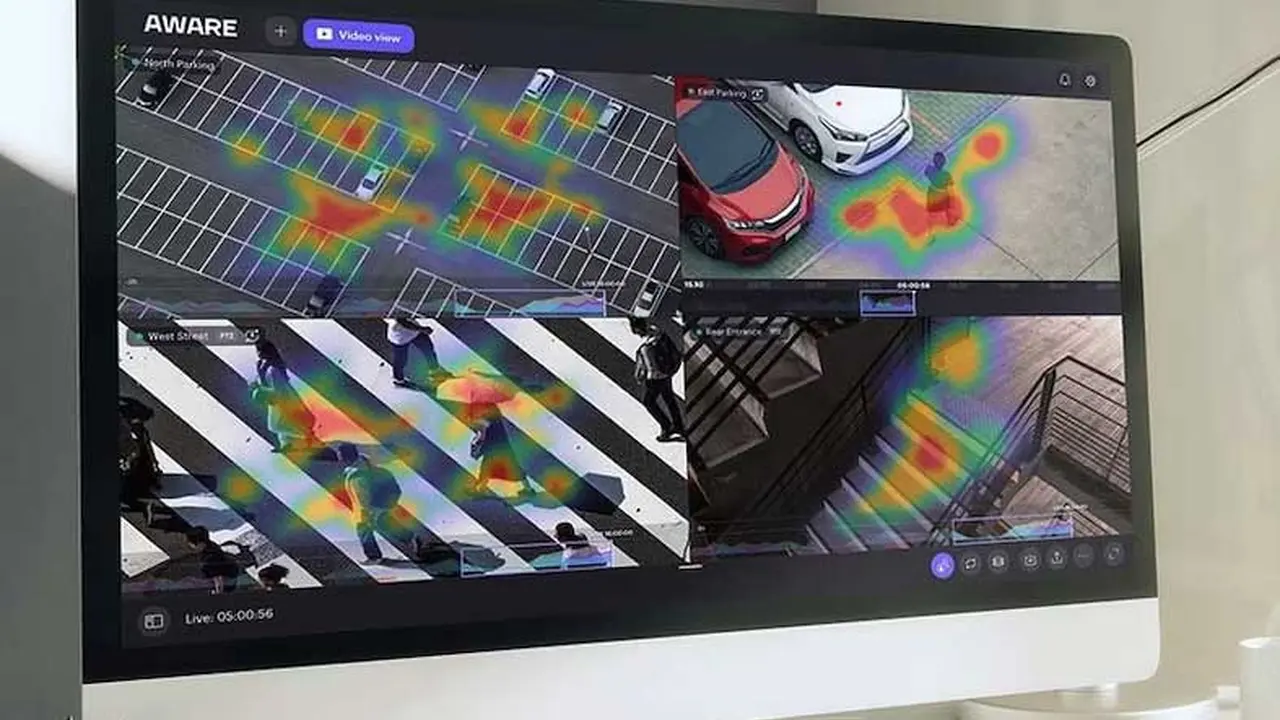
- Video Surveillance (CCTV) Systems: Monitoring activities, recording footage, and providing visual verification of events. Modern systems often include advanced analytics like facial recognition, object detection, and anomaly detection.
- Intrusion Detection and Alarm Systems: Sensors and alarms that detect unauthorized entry, movement, or environmental changes (e.g., smoke, flood).
- Perimeter Security: Fences, gates, sensors, and surveillance along the facility's boundaries to detect and deter external threats.
- Intercom and Communication Systems: Enabling two-way communication at entry points or within secure areas.
- Visitor Management Systems: Streamlining the process of registering, tracking, and managing visitors, often integrated with access control.
- Physical Security Information Management (PSIM) and Security Information and Event Management (SIEM) Software: These are the brains of the operation, collecting data from all integrated systems, correlating events, and presenting a unified operational picture to security personnel. PSIM focuses on physical security, while SIEM often includes cybersecurity aspects.
- Emergency Management and Mass Notification Systems: Tools for quickly disseminating critical information during emergencies and coordinating response efforts.
- Cybersecurity Integration: Protecting the security network itself from cyber threats, which is increasingly crucial as physical security systems become more IP-based.
Key Features and Compliance Requirements for Government Security
When it comes to government facilities, security solutions must meet stringent requirements that go beyond typical commercial needs. Here are some critical features and compliance considerations:Robust Access Control and Identity Management
Government facilities require granular control over who can access specific areas. This means multi-factor authentication (MFA) is often a standard, combining something you know (PIN), something you have (smart card, mobile credential), and something you are (biometrics like fingerprint or iris scan). The system must support various credential types, including PIV (Personal Identity Verification) cards for federal employees, and be able to manage temporary access for contractors and visitors with strict expiration policies. Integration with HR databases for automated onboarding and offboarding is also crucial.Advanced Video Surveillance and Analytics
High-resolution cameras (4K, thermal, panoramic) are essential for clear identification and wide-area coverage. Video analytics play a vital role, including:- Facial Recognition: For identifying authorized personnel or flagging individuals on watchlists.
- License Plate Recognition (LPR): For vehicle access control and monitoring.
- Object Detection and Tracking: Identifying unattended packages or suspicious activities.
- Behavioral Analytics: Detecting unusual patterns or aggressive behavior.
- Intrusion Detection: Virtual tripwires and zone monitoring.
Intrusion Detection and Perimeter Security
Beyond standard door/window sensors, government facilities often employ advanced perimeter detection technologies such as:- Fiber Optic Fence Sensors: Detecting vibrations along fences.
- Ground Radar and Buried Cable Sensors: Detecting movement underground or on the surface.
- Thermal Cameras: Effective for detecting intruders in low-light or adverse weather conditions.
- Drone Detection Systems: Identifying and potentially neutralizing unauthorized drones.
Cybersecurity and Data Protection
As physical security systems become more networked, they become potential entry points for cyberattacks. Integrated solutions must incorporate robust cybersecurity measures, including:- End-to-End Encryption: Protecting data in transit and at rest.
- Network Segmentation: Isolating security networks from general IT networks.
- Regular Vulnerability Assessments and Penetration Testing: Proactively identifying and addressing weaknesses.
- Compliance with NIST, FIPS, and other government cybersecurity standards.
Redundancy and Resilience
Government operations cannot afford downtime. Integrated systems must be designed with high availability, including redundant servers, power supplies, and network connections. Disaster recovery plans and off-site backups are also critical.Regulatory Compliance
Government facilities must adhere to a myriad of regulations, which vary by agency and jurisdiction. Common compliance requirements include:- FIPS 201 (Federal Information Processing Standard Publication 201): Mandates the use of PIV cards for federal employees and contractors.
- NIST SP 800 Series: Guidelines for information security, often applied to physical security systems that handle sensitive data.
- HIPAA (Health Insurance Portability and Accountability Act): For healthcare-related government facilities, protecting patient data.
- CMMC (Cybersecurity Maturity Model Certification): For Department of Defense contractors, ensuring robust cybersecurity practices.
- Local and State Regulations: Specific building codes, fire safety, and emergency response protocols.
Recommended Integrated Security Solutions and Products
Choosing the right integrated security solution for a government facility involves careful consideration of scale, existing infrastructure, budget, and specific security needs. Here are some leading providers and their offerings, along with typical use cases and pricing considerations.1. Genetec Security Center
Genetec Security Center is a unified security platform that seamlessly blends IP video surveillance (VMS), access control (ACS), automatic license plate recognition (ALPR), and communications. It's highly scalable and designed for mission-critical applications, making it a strong contender for large government facilities and multi-site deployments.- Key Features: Unified VMS, ACS, and ALPR; advanced video analytics; robust cybersecurity features; open architecture for third-party integrations; FIPS 201 compliance; mobile access.
- Use Cases: Federal agencies, state capitols, large municipal complexes, critical infrastructure (e.g., power plants, water treatment facilities), transportation hubs.
- Specific Products/Modules: Omnicast (VMS), Synergis (ACS), AutoVu (ALPR).
- Comparison: Known for its open architecture, allowing integration with a vast array of cameras, readers, and other hardware from different manufacturers. This provides flexibility and avoids vendor lock-in. Its scalability is excellent for growing needs.
- Pricing: Enterprise-grade solution, so expect significant investment. Licensing is typically per device (camera, door reader) and per module. A small deployment might start from tens of thousands of dollars, while large federal projects can easily run into millions, including hardware, software, installation, and ongoing support.
2. LenelS2 OnGuard
LenelS2 OnGuard is another industry-leading integrated security platform, particularly strong in access control but also offering robust video management and intrusion detection capabilities. It's widely used in government and corporate environments due to its reliability and comprehensive feature set.- Key Features: Powerful access control with FIPS 201/PIV support; comprehensive video management; visitor management; alarm monitoring; mobile credentials; strong reporting and auditing tools.
- Use Cases: Department of Defense facilities, government research labs, secure administrative buildings, courthouses.
- Specific Products/Modules: OnGuard Access, OnGuard Video, OnGuard Visitor.
- Comparison: LenelS2 is often praised for its deep access control capabilities and strong compliance features, making it a go-to for highly secure environments. While it supports integrations, it might be slightly less open than Genetec in some aspects, often favoring its own hardware or certified partners.
- Pricing: Similar to Genetec, OnGuard is an enterprise solution. Costs depend on the number of doors, cameras, and modules required. Expect a substantial investment, with projects ranging from high five figures to multi-million dollar deployments.
3. Johnson Controls C•CURE 9000
Johnson Controls (formerly Tyco Security Products) offers C•CURE 9000, a powerful and flexible security management system that integrates access control, video, intrusion, and other business systems. It's designed for complex environments requiring high levels of security and operational efficiency.- Key Features: Advanced access control with FIPS 201/PIV support; robust event management; video integration with exacqVision and American Dynamics; visitor management; mobile access; extensive reporting.
- Use Cases: Government office buildings, correctional facilities, public safety centers, critical infrastructure.
- Specific Products/Modules: C•CURE 9000 Access Control, victor Unified Client (for video and event management).
- Comparison: C•CURE 9000 is known for its user-friendly interface and powerful event management capabilities, allowing operators to quickly respond to incidents. It integrates well with other Johnson Controls building management systems, which can be an advantage for facilities looking for broader smart building solutions.
- Pricing: Enterprise-level pricing, comparable to Genetec and LenelS2. The total cost will be influenced by the scale of the deployment, hardware choices, and specific software modules.
4. Bosch Building Integration System (BIS)
Bosch BIS is a comprehensive security and building management platform that integrates various Bosch security products (access control, video surveillance, intrusion detection, fire alarms) with third-party systems. It's particularly strong for facilities that require a holistic approach to building management alongside security.- Key Features: Unified management of security, fire, and building automation; modular and scalable; advanced video analytics; FIPS 201 compliance; robust reporting.
- Use Cases: Government administrative buildings, public libraries, museums, educational institutions, transportation facilities.
- Specific Products/Modules: BIS Access Engine, BIS Video Engine, BIS Intrusion Engine.
- Comparison: Bosch's strength lies in its ability to integrate not just security but also fire safety and building automation (HVAC, lighting) into a single platform. This can lead to significant operational efficiencies for facilities looking for a truly smart building solution.
- Pricing: As an enterprise solution, pricing is project-specific and depends on the scope of integration. Expect costs in the range of high five figures to several millions for large-scale government deployments.
5. Honeywell Pro-Watch Integrated Security Suite
Honeywell's Pro-Watch is an enterprise-class security management system that provides advanced access control, video surveillance, and intrusion detection capabilities. It's designed for high-security applications and offers strong compliance features.- Key Features: Scalable access control with FIPS 201/PIV support; comprehensive video management; visitor management; alarm monitoring; mobile access; strong audit trails.
- Use Cases: Federal government facilities, critical infrastructure, airports, seaports, correctional facilities.
- Specific Products/Modules: Pro-Watch Access, Pro-Watch Video, Pro-Watch Visitor.
- Comparison: Honeywell is a well-established name in security and building technologies. Pro-Watch is known for its reliability and robust feature set, particularly in highly regulated environments. It integrates well with other Honeywell products, offering a comprehensive solution for those already invested in the Honeywell ecosystem.
- Pricing: Enterprise-level pricing, similar to other major players. Costs will vary based on the number of access points, cameras, and specific modules implemented.
:max_bytes(150000):strip_icc()/277019-baked-pork-chops-with-cream-of-mushroom-soup-DDMFS-beauty-4x3-BG-7505-5762b731cf30447d9cbbbbbf387beafa.jpg)