Integrated Security Solutions with Cybersecurity Integration
Discover integrated security solutions that combine physical and cybersecurity measures for holistic protection.
Discover integrated security solutions that combine physical and cybersecurity measures for holistic protection.
Integrated Security Solutions with Cybersecurity Integration
Hey there! Let's talk about something super important in today's world: keeping everything safe and sound. We're not just talking about locking your doors anymore. We're talking about a comprehensive approach that blends physical security – think cameras and access cards – with the digital kind, cybersecurity. This combo is what we call integrated security solutions with cybersecurity integration, and it's becoming absolutely essential for businesses, governments, and even advanced homes.
Why is this such a big deal? Well, in the past, physical security and cybersecurity were often treated as separate entities. You had one team managing the guards and cameras, and another team handling firewalls and data encryption. But here's the kicker: these two worlds are increasingly intertwined. A physical breach can lead to a cyberattack, and a cyberattack can facilitate a physical breach. Imagine someone hacking into your access control system to open doors, or using a compromised network camera to spy on sensitive documents. See? The lines are blurring, and that's why integration is key.
This article is going to dive deep into how these integrated systems work, why they're so crucial, and what kind of solutions are out there. We'll look at some real-world examples, discuss the benefits, and even recommend some specific products and their use cases. So, buckle up!
Understanding Integrated Security Physical and Cyber Convergence
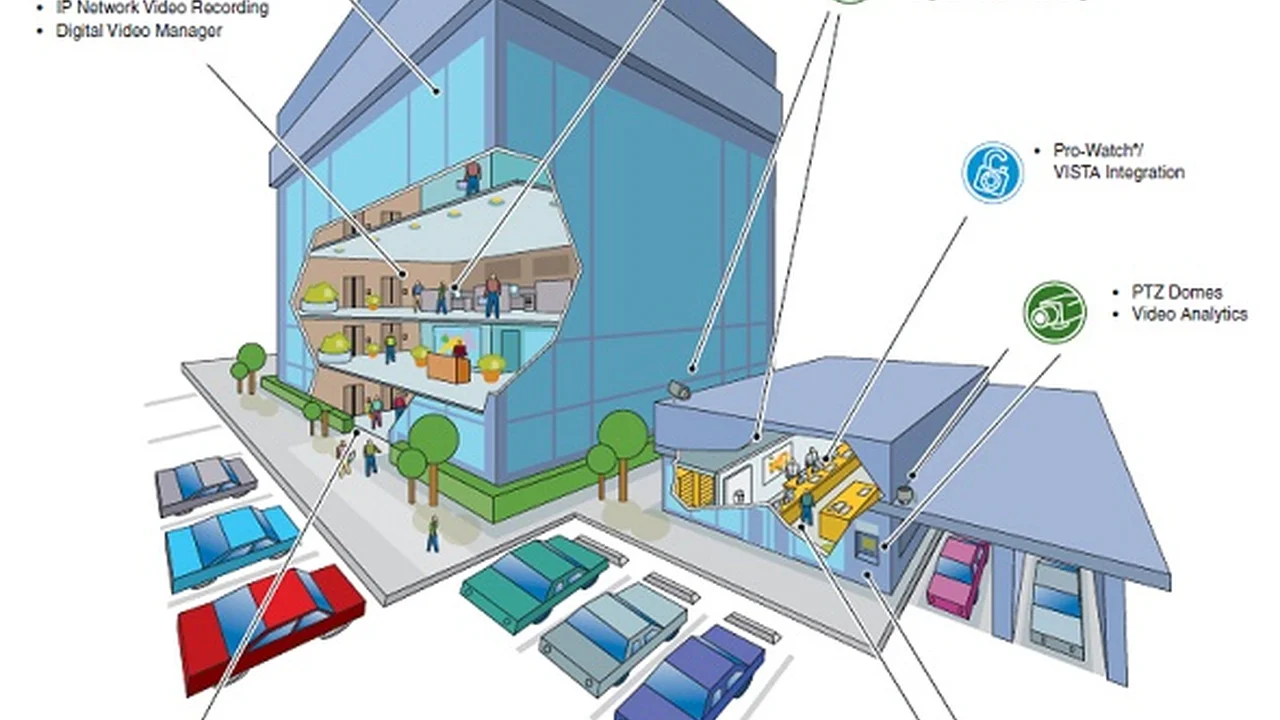
So, what exactly does 'physical and cyber convergence' mean? It's basically the idea that physical security systems (like surveillance, access control, and alarm systems) and cybersecurity systems (like network security, data protection, and threat intelligence) are no longer operating in silos. Instead, they're designed to work together, sharing information and coordinating responses to threats.
Think of it like this: your physical security system might detect an unauthorized person trying to enter a restricted area. If this system is integrated with your cybersecurity, it could immediately trigger an alert to the IT security team, lock down network access for devices in that area, and even initiate a data backup. Conversely, if your cybersecurity system detects a malware attack on a server, it could alert physical security to increase surveillance around the server room, or even restrict physical access to that area until the threat is neutralized.
This convergence offers a much more holistic view of security. Instead of two separate teams reacting to isolated incidents, you have a unified front that can anticipate, detect, and respond to threats more effectively, regardless of whether they originate in the physical or digital realm.
Key Components of Integrated Security Solutions Cybersecurity Integration
When we talk about integrated security solutions with cybersecurity integration, we're looking at a blend of several technologies. Here are some of the core components:
Access Control Systems Integrated with Network Security
Access control is all about who gets in and out of your physical spaces. Traditionally, this meant key cards or biometric scanners. But when integrated with network security, it gets a whole lot smarter. Imagine an employee's access card being deactivated not just because they left the company, but also because their network credentials were compromised. Or, if a user tries to access a sensitive server, the system might require a physical biometric scan in addition to their digital login.
Products to consider:
- HID Global pivCLASS: This system offers strong authentication for both physical and logical access, often used in government and high-security environments. It integrates physical access control with digital identity management, ensuring that only authorized personnel with valid credentials can access both physical spaces and IT systems.
- LenelS2 OnGuard: A comprehensive access control platform that can be integrated with various IT security tools. It allows for centralized management of physical access, video surveillance, and alarm monitoring, and can share data with cybersecurity platforms to correlate events.
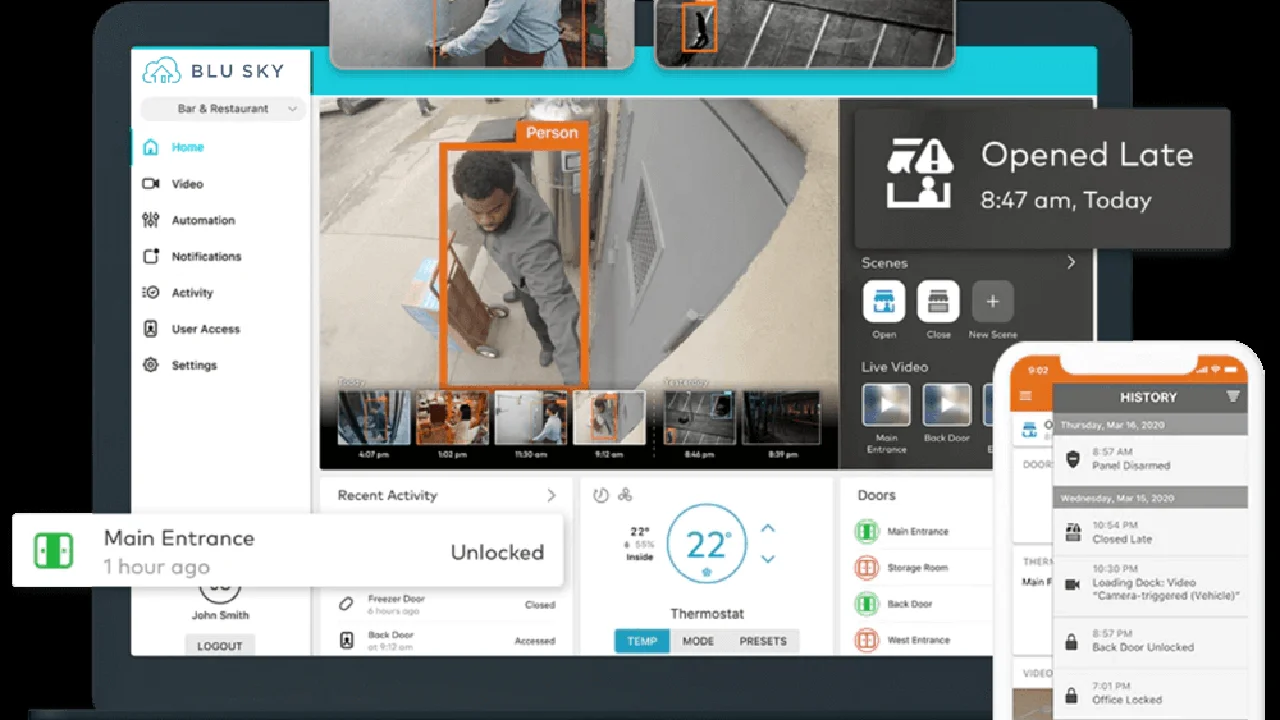
Video Surveillance Systems with Cyber Threat Detection
Modern video surveillance isn't just about recording footage anymore. With AI and analytics, cameras can detect unusual behavior, identify individuals, and even flag potential threats. When integrated with cybersecurity, these systems can become even more powerful. For example, if a camera detects someone tampering with a server rack, it could not only alert physical security but also trigger a network scan for vulnerabilities or unauthorized access attempts in that area.
Conversely, if a cyberattack is detected, the system could automatically direct cameras to focus on critical infrastructure or entry points, providing visual confirmation of any physical activity related to the cyber incident.
Products to consider:
- Axis Communications with AXIS Camera Station: Axis cameras are known for their robust security features and can be integrated with various video management systems (VMS) that offer advanced analytics. Some VMS solutions can integrate with SIEM (Security Information and Event Management) systems to correlate video events with cyber alerts.
- Genetec Security Center: This is a unified security platform that seamlessly blends video surveillance, access control, and license plate recognition. It has strong API capabilities, allowing integration with cybersecurity tools for a truly converged security approach. For instance, if a cyber threat is detected on a specific network segment, Genetec could automatically pull up camera feeds from that area.
Intrusion Detection Systems Integrated with Network Monitoring
Intrusion detection systems (IDS) are designed to detect unauthorized entry into physical spaces. When these systems are integrated with network monitoring tools, they can provide a more complete picture of a potential breach. If a physical intrusion is detected, the system could automatically increase network monitoring for unusual activity, looking for signs of data exfiltration or internal network compromise.
Similarly, if network monitoring detects a suspicious login attempt from an unusual location, it could trigger an alert to physical security to check the physical presence of the user at their workstation or in the building.
Products to consider:
- Honeywell Pro-Watch: This is an integrated security suite that combines access control, intrusion detection, and video surveillance. It can be configured to send alerts to network security teams based on physical events, and its open architecture allows for integration with various IT systems.
- Bosch Security Systems: Bosch offers a wide range of intrusion detection panels and sensors that can be integrated into larger security management systems. Their solutions often include IP-based communication, making it easier to connect with network security platforms.
Security Information and Event Management SIEM for Unified Threat Intelligence
SIEM systems are the brains of the operation when it comes to cybersecurity. They collect and analyze security event data from various sources across an organization's IT infrastructure. When integrated with physical security systems, SIEM can become a powerful tool for unified threat intelligence.
Imagine a SIEM system receiving alerts from both your firewall (cyber) and your access control system (physical). It can then correlate these events to identify patterns or anomalies that might indicate a sophisticated attack. For example, if a failed login attempt on a critical server (cyber event) is immediately followed by an unauthorized attempt to open the server room door (physical event), the SIEM can flag this as a high-priority incident requiring immediate attention.
Products to consider:
- Splunk Enterprise Security: A leading SIEM solution that can ingest data from virtually any source, including physical security systems. It provides powerful analytics and correlation capabilities to identify complex threats that span both physical and cyber domains.
- IBM QRadar: Another top-tier SIEM that offers robust threat detection and incident response. QRadar can integrate with physical security systems through APIs or syslog, allowing it to correlate physical events with network and application logs.
- Microsoft Sentinel: A cloud-native SIEM from Microsoft that leverages AI and machine learning to detect threats. It can integrate with various data sources, including physical security systems, to provide a unified view of security posture.
Benefits of Integrated Security Solutions with Cybersecurity Integration
So, why go through all this trouble to integrate everything? The benefits are pretty compelling:
Enhanced Threat Detection and Response Integrated Security
This is probably the biggest one. By combining physical and cyber data, you get a much clearer and more complete picture of potential threats. This leads to faster and more accurate detection, and allows for a more coordinated and effective response. You can move from reactive to proactive security, anticipating threats before they fully materialize.
Improved Operational Efficiency and Cost Savings
When your systems are integrated, your security teams can work more efficiently. Instead of managing separate platforms and responding to isolated alerts, they have a single pane of glass view of all security events. This reduces manual effort, minimizes human error, and can lead to significant cost savings in terms of staffing and resource allocation.
Reduced Risk and Compliance Adherence
A converged security approach significantly reduces your overall risk profile. By addressing vulnerabilities that span both physical and cyber domains, you're better protected against a wider range of attacks. Plus, many regulatory compliance frameworks (like GDPR, HIPAA, and various industry standards) are increasingly requiring organizations to demonstrate a holistic approach to security, making integration a key factor in meeting these requirements.
Better Situational Awareness and Decision Making
With all security data flowing into a central platform, decision-makers have much better situational awareness. They can see how physical events might impact cyber assets and vice versa, allowing them to make more informed and strategic decisions about security investments and incident response.
Real-World Use Cases for Integrated Security Cybersecurity
Let's look at some practical examples of where integrated security solutions with cybersecurity integration really shine:
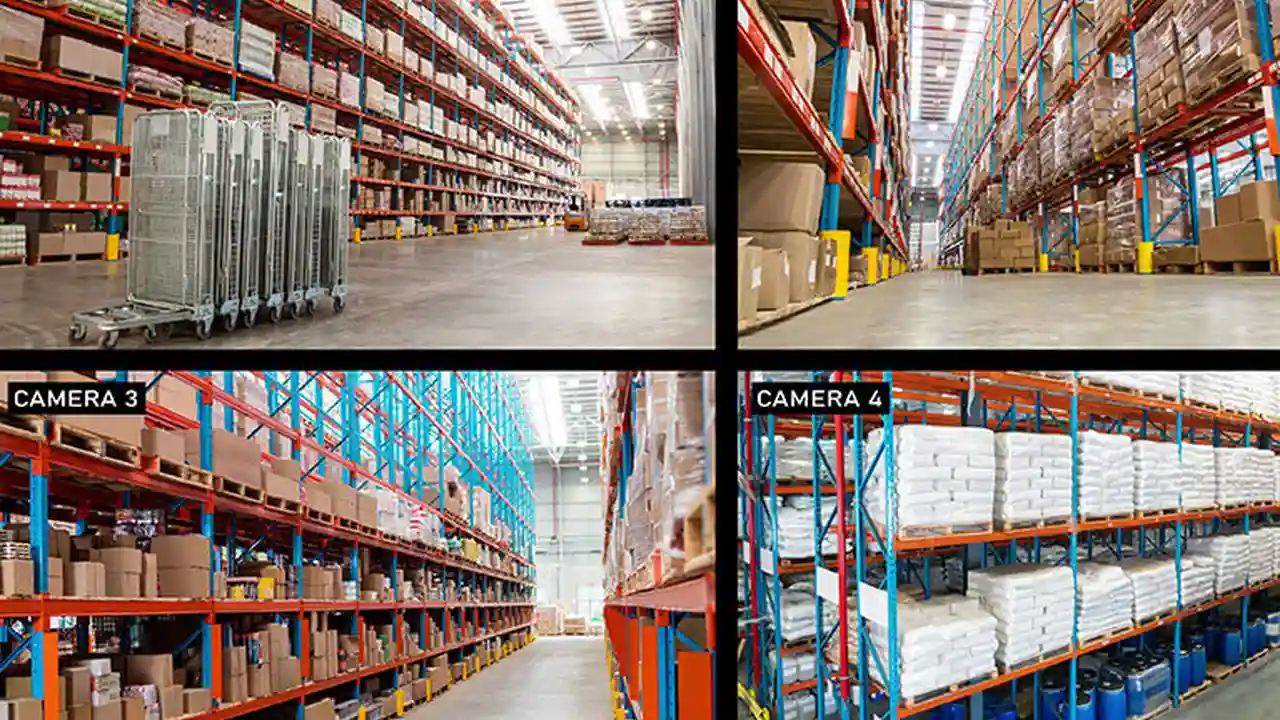
Data Centers and Critical Infrastructure Protection
Data centers are prime targets for both physical and cyberattacks. An integrated system here would mean that physical access control to server rooms is tightly linked with network access policies. If an unauthorized person attempts to enter, not only are alarms triggered, but network access to critical servers in that area might be temporarily restricted. Conversely, if a cyberattack is detected on a specific server, physical security cameras could automatically focus on that server's location, and access to the room could be locked down.
Corporate Campuses and Office Buildings
In a corporate setting, an integrated system could track employee movements (physical access) and correlate them with their network activity. If an employee tries to access a highly sensitive document from a location they shouldn't physically be in, the system could flag it. Or, if a terminated employee's network access is revoked, their physical access card could also be automatically deactivated, preventing them from entering the building.
Healthcare Facilities and Patient Data Security
Healthcare facilities deal with highly sensitive patient data, making them targets for both physical theft and cyber breaches. Integrated security ensures that access to patient records (digital) is tied to physical access to areas where those records are stored or accessed. For example, a doctor's access badge might only grant them access to specific patient wards and also allow them to access patient files on the network from designated workstations within those wards. Any deviation could trigger an alert.
Smart Cities and Public Safety
In smart cities, integrated security can play a crucial role in public safety. Imagine traffic cameras (physical) detecting an unusual gathering, and this information being fed into a system that also monitors social media for cyber threats or public unrest. This allows authorities to respond more quickly and effectively to potential incidents, whether they start online or in the physical world.
Comparing Integrated Security Solutions and Their Pricing
Choosing the right integrated security solution can be tricky, as it often depends on the scale of your operations, your specific needs, and your budget. Here's a general comparison of some leading solutions, keeping in mind that pricing can vary wildly based on customization, number of devices, and ongoing service contracts.
For Small to Medium Businesses (SMBs)
SMBs often need solutions that are relatively easy to deploy and manage, without breaking the bank. They might not need the full complexity of enterprise-grade systems but still benefit from some level of integration.
-
Product: Verkada Command Platform
- Description: Verkada offers a cloud-based platform that integrates video security, access control, environmental sensors, and alarm systems. It's known for its ease of use and plug-and-play installation.
- Cybersecurity Integration: While primarily a physical security platform, Verkada's cloud-native nature means it adheres to strong cybersecurity practices for data transmission and storage. It also offers API integrations that can push alerts to SIEM systems or other cybersecurity platforms.
- Use Case: Retail stores, small office buildings, schools.
- Estimated Pricing: Starts from a few thousand dollars for basic hardware and software licenses, scaling up with more cameras, doors, and features. Annual subscription fees are typical.
- Pros: Simple to deploy, cloud-managed, good analytics, strong physical security features.
- Cons: Can become expensive at scale, less granular cybersecurity integration compared to enterprise solutions.
-
Product: Open-Source Integrations (e.g., Home Assistant with Security Add-ons)
- Description: For tech-savvy SMBs or advanced home users, open-source platforms like Home Assistant can be customized to integrate various physical security devices (cameras, sensors, smart locks) with network monitoring tools.
- Cybersecurity Integration: This is highly customizable. You can integrate with open-source SIEM alternatives like ELK Stack (Elasticsearch, Logstash, Kibana) or even simple scripts that monitor network traffic and trigger physical security responses.
- Use Case: Small offices, advanced home security, proof-of-concept projects.
- Estimated Pricing: Primarily hardware costs, as software is free. Time investment for setup and maintenance is significant.
- Pros: Highly flexible, no recurring software fees, complete control over data.
- Cons: Requires significant technical expertise, no commercial support, can be less robust than commercial solutions.
For Enterprises and Large Organizations
Large organizations require robust, scalable, and highly customizable solutions that can handle complex integrations and stringent compliance requirements.
-
Product: Genetec Security Center with Cybersecurity Integrations
- Description: Genetec Security Center is a unified security platform that brings together video surveillance, access control, ANPR (Automatic Number Plate Recognition), and communications. It's designed for large-scale deployments and offers extensive integration capabilities.
- Cybersecurity Integration: Genetec offers a robust SDK and APIs that allow deep integration with leading SIEM platforms (Splunk, QRadar, Sentinel), network access control (NAC) solutions, and identity management systems. This enables real-time data exchange and coordinated responses between physical and cyber domains.
- Use Case: Airports, critical infrastructure, large corporate campuses, government facilities.
- Estimated Pricing: Enterprise-level pricing, typically starting from tens of thousands to hundreds of thousands of dollars, depending on the modules, number of devices, and customization. Annual maintenance and support contracts are standard.
- Pros: Highly scalable, comprehensive feature set, strong integration capabilities, robust and reliable.
- Cons: High initial investment, requires specialized expertise for deployment and management.
-
Product: LenelS2 OnGuard with Cyber Integration Modules
- Description: LenelS2 OnGuard is another powerful, enterprise-grade access control and security management system. It's known for its reliability and extensive feature set, including visitor management, alarm monitoring, and video integration.
- Cybersecurity Integration: LenelS2 offers specific modules and partnerships for cybersecurity integration, allowing OnGuard to share event data with SIEM systems, identity and access management (IAM) platforms, and network security tools. This enables a unified view of security events and automated responses.
- Use Case: Large corporations, government, healthcare, education.
- Estimated Pricing: Similar to Genetec, enterprise-level pricing, often requiring custom quotes based on project scope.
- Pros: Very robust, highly customizable, strong compliance features, extensive partner ecosystem.
- Cons: Complex to deploy, high cost, requires dedicated IT and security teams.
-
Product: Siemens Siveillance Suite
- Description: Siemens offers a comprehensive suite of security management solutions under the Siveillance brand, covering access control, video surveillance, and intrusion detection. It's designed for complex, large-scale environments.
- Cybersecurity Integration: Siveillance solutions are built with cybersecurity in mind, offering secure communication protocols and integration capabilities with IT security platforms. They can feed physical security events into SIEM systems for correlation and analysis, enhancing overall threat intelligence.
- Use Case: Industrial facilities, critical infrastructure, large public venues.
- Estimated Pricing: High-end enterprise solution, custom quotes based on project complexity.
- Pros: Extremely reliable, designed for critical environments, strong focus on data integrity and security.
- Cons: Very high cost, complex implementation, requires specialized Siemens expertise.
Challenges and Considerations for Integrated Security Cybersecurity
While the benefits are clear, integrating physical and cybersecurity isn't without its challenges. Here are a few things to keep in mind:
Complexity of Integration and Interoperability
Getting different systems from different vendors to talk to each other seamlessly can be a huge headache. You're dealing with different protocols, APIs, and data formats. This often requires significant custom development or reliance on vendors who offer open architectures and robust integration capabilities.
Data Privacy and Compliance Concerns
When you start combining physical security data (like video footage of individuals) with cybersecurity data (like network activity), you're dealing with a lot of sensitive information. Ensuring compliance with data privacy regulations (like GDPR or CCPA) becomes even more critical. You need clear policies on data collection, storage, access, and retention.
Organizational Silos and Skill Gaps
Often, physical security and IT security teams operate in different departments with different reporting structures and skill sets. Breaking down these organizational silos and fostering collaboration is crucial for successful integration. You might also need to invest in training to bridge skill gaps, ensuring both teams understand the nuances of the other's domain.
Cost and Return on Investment
Implementing integrated security solutions can be a significant investment. It's important to clearly define your objectives, assess the risks, and build a strong business case to demonstrate the return on investment (ROI). This isn't just about preventing losses; it's also about improving operational efficiency and maintaining compliance.
The Future of Integrated Security Solutions with Cybersecurity Integration
Looking ahead, the convergence of physical and cybersecurity is only going to accelerate. We can expect to see even more sophisticated integrations driven by advancements in:
- Artificial Intelligence (AI) and Machine Learning (ML): AI and ML will play an even bigger role in analyzing vast amounts of data from both physical and cyber sources, identifying subtle patterns, predicting threats, and automating responses.
- Internet of Things (IoT) Security: As more physical devices become connected to networks, securing the IoT ecosystem will be paramount. Integrated solutions will be crucial for managing the security of these devices, from smart sensors to autonomous vehicles.
- Cloud-Native Security Platforms: More security solutions will move to the cloud, offering greater scalability, flexibility, and easier integration with other cloud services.
- Zero Trust Architectures: The 'never trust, always verify' principle of Zero Trust will extend beyond network access to physical access, requiring continuous authentication and authorization for both users and devices.
Ultimately, the goal is to create a truly resilient security posture that can withstand the evolving threat landscape. By bringing physical and cybersecurity together, organizations can build a more robust, efficient, and intelligent defense system. It's not just about protecting assets; it's about ensuring business continuity and maintaining trust in an increasingly interconnected world. So, if you're thinking about your security strategy, remember: integration isn't just a buzzword; it's the future.
:max_bytes(150000):strip_icc()/277019-baked-pork-chops-with-cream-of-mushroom-soup-DDMFS-beauty-4x3-BG-7505-5762b731cf30447d9cbbbbbf387beafa.jpg)