Understanding the Components of an Integrated Security System
Learn about the various components that make up an integrated security system and how they work together.
Understanding the Components of an Integrated Security System
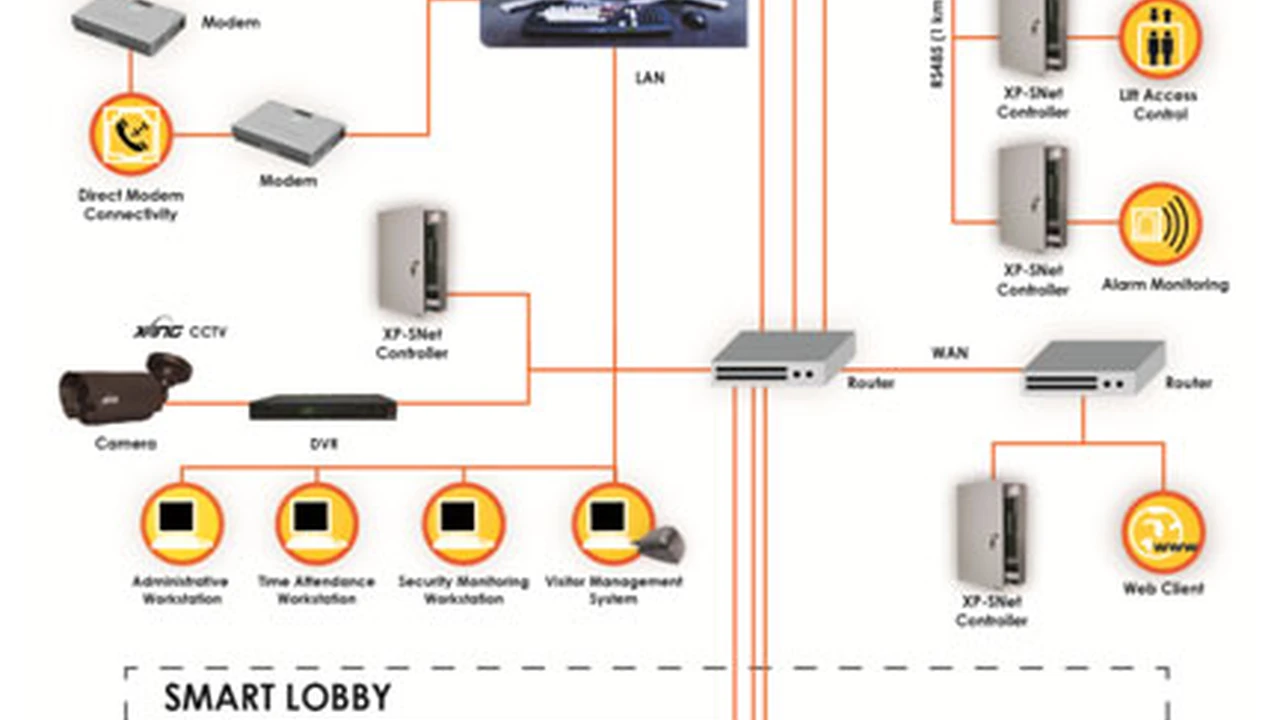
Integrated security systems are the backbone of modern protection strategies for businesses, institutions, and even large residential complexes. They move beyond simply having a collection of security devices by creating a cohesive, interconnected network where each component communicates and collaborates. This synergy leads to a more effective, efficient, and proactive security posture. Let's dive deep into the essential components that form these powerful systems.
The Central Nervous System The Security Management Platform
At the heart of every integrated security system lies the Security Management Platform (SMP), often referred to as a Physical Security Information Management (PSIM) system or a unified security platform. This is the brain that collects, processes, and correlates data from all connected security devices. Think of it as the operating system for your entire security infrastructure.
Key Functions of an SMP:
- Centralized Monitoring: Provides a single interface for viewing live feeds, alarm statuses, and access events from all connected systems.
- Event Correlation: Analyzes data from different sources to identify patterns or potential threats that individual systems might miss. For example, a door forced open (access control) combined with motion detection (CCTV) in the same area triggers a higher-priority alert.
- Automated Workflows: Enables the creation of predefined responses to specific events, such as locking doors, activating alarms, or sending notifications to security personnel.
- Reporting and Analytics: Generates detailed reports on security events, system performance, and compliance, aiding in forensic investigations and future planning.
- User Management: Manages user permissions and access levels across all integrated systems.
Recommended SMP Products:
-
Genetec Security Center:
- Description: A highly scalable and robust unified security platform that seamlessly integrates video surveillance, access control, ANPR (Automatic Number Plate Recognition), and communications. It's known for its open architecture and extensive third-party integrations.
- Use Case: Ideal for large enterprises, critical infrastructure, airports, and smart city initiatives requiring a comprehensive, future-proof solution.
- Pricing: Varies significantly based on modules, number of devices, and licensing. Typically starts in the tens of thousands of dollars for a basic enterprise setup and can go into the hundreds of thousands.
-
LenelS2 OnGuard:
- Description: A powerful and widely adopted access control and security management system. While primarily known for access control, it offers strong integration capabilities with video, intrusion, and other building management systems.
- Use Case: Popular in corporate campuses, government facilities, and healthcare environments where robust access control and compliance are paramount.
- Pricing: Similar to Genetec, pricing is project-specific and depends on the scale and features. Expect significant investment for enterprise deployments.
-
Milestone XProtect (with add-ons):
- Description: While primarily a Video Management Software (VMS), Milestone's open platform allows for extensive integration with access control, analytics, and other security systems through its Marketplace. It can function as a powerful central hub for video-centric integrated solutions.
- Use Case: Excellent for organizations prioritizing advanced video surveillance but also needing to integrate other security functions. Suitable for retail, education, and manufacturing.
- Pricing: XProtect base licenses can range from a few hundred dollars for small systems to several thousand for enterprise versions, with integration add-ons costing extra.
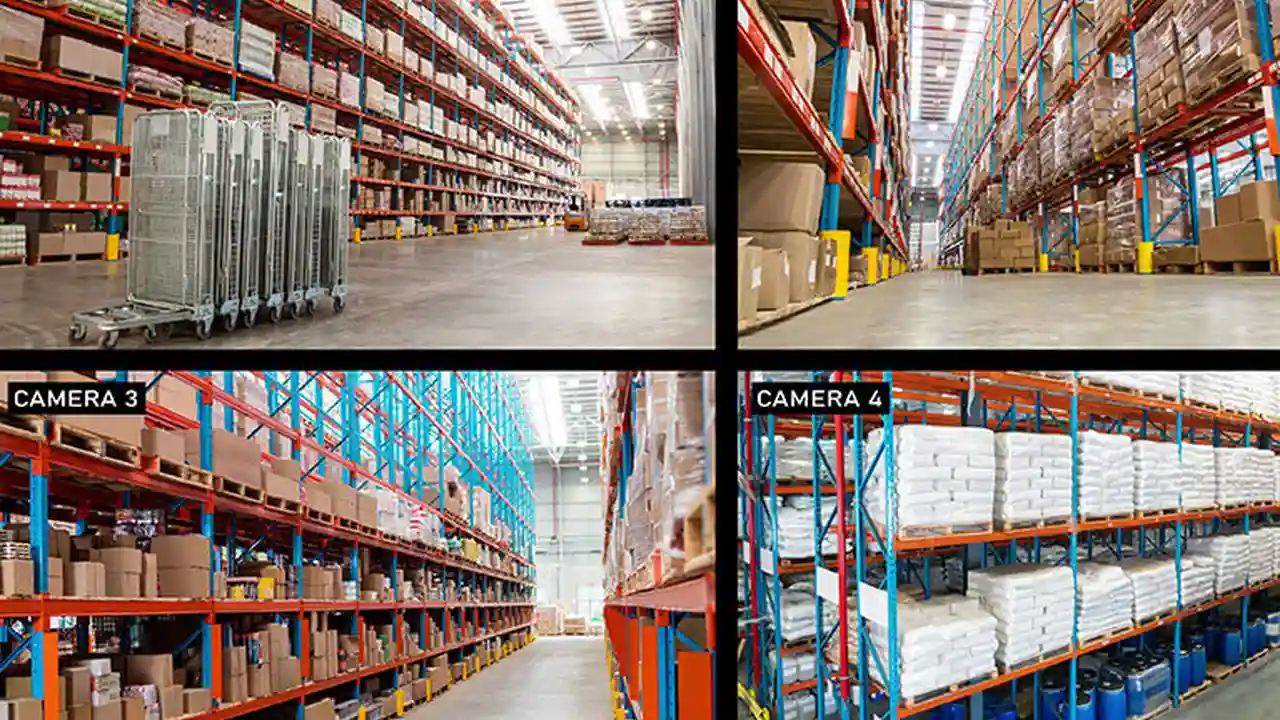
Eyes Everywhere Video Surveillance Systems CCTV
Video surveillance, or CCTV (Closed-Circuit Television), is a cornerstone of any security system. In an integrated setup, CCTV cameras are not just recording devices; they are intelligent sensors providing visual verification and triggering events.
Key Aspects of Integrated CCTV:
- IP Cameras: Modern systems predominantly use IP (Internet Protocol) cameras for higher resolution, easier scalability, and network connectivity.
- Video Analytics: Integrated systems leverage advanced video analytics (e.g., motion detection, facial recognition, object tracking, perimeter intrusion detection) to turn raw video data into actionable intelligence.
- Event-Driven Recording: Cameras can be configured to record only when specific events occur (e.g., motion, door forced open), saving storage and making review more efficient.
- Remote Access: Security personnel can view live and recorded footage from anywhere, anytime, via secure network connections.
Recommended CCTV Products:
-
Axis Communications IP Cameras:
- Description: A global leader in network video, Axis offers a vast range of high-quality IP cameras (dome, bullet, PTZ, thermal) known for their reliability, image quality, and advanced analytics capabilities.
- Use Case: Versatile for almost any application, from small businesses to large-scale critical infrastructure. Their open platform ensures broad compatibility with VMS and SMPs.
- Pricing: Entry-level cameras start around $200-$300, with advanced models (PTZ, thermal) ranging from $1,000 to several thousand dollars.
-
Hikvision and Dahua IP Cameras:
- Description: These Chinese manufacturers offer a wide array of cost-effective IP cameras with competitive features, including high resolution, night vision, and built-in analytics. They are popular for their value proposition.
- Use Case: Suitable for businesses and organizations looking for feature-rich surveillance solutions at a more accessible price point. Widely used in retail, small to medium enterprises, and residential complexes.
- Pricing: Entry-level cameras can be found for under $100, with more advanced models typically in the $200-$800 range.
Controlling Entry and Exit Access Control Systems
Access control systems manage who can go where and when. In an integrated environment, access events are logged, correlated with video, and can trigger other security responses.
Key Features of Integrated Access Control:
- Credential Management: Supports various credentials like key cards, fobs, mobile credentials, and biometrics (fingerprint, facial recognition).
- Real-time Monitoring: Provides instant alerts for unauthorized access attempts, forced entries, or propped-open doors.
- Integration with HR Systems: Can automatically update access rights based on employee status (e.g., new hire, termination).
- Lockdown Capabilities: Allows for immediate lockdown of specific areas or an entire facility in an emergency.
Recommended Access Control Products:
-
HID Global (Readers and Credentials):
- Description: A leading provider of secure identity solutions, HID offers a vast range of access control readers (proximity, smart card, biometric) and credentials (cards, fobs, mobile IDs) known for their security and interoperability.
- Use Case: Essential for any access control system, providing the physical interface for users to gain entry. Widely used across all sectors.
- Pricing: Readers typically range from $100 to $500+, with credentials costing a few dollars each.
-
Mercury Security (Controllers):
- Description: Mercury provides open-architecture access control hardware (controllers and panels) that are compatible with a multitude of software platforms, offering flexibility and scalability.
- Use Case: Preferred by integrators and end-users who want to avoid vendor lock-in and build highly customized access control solutions.
- Pricing: Controllers can range from $500 to several thousand dollars depending on capacity and features.
-
Brivo Access:
- Description: A pioneer in cloud-based access control, Brivo offers a scalable, easy-to-manage solution with strong mobile capabilities and integrations.
- Use Case: Excellent for businesses of all sizes, especially those with multiple locations or a need for remote management. Popular in commercial real estate, co-working spaces, and tech companies.
- Pricing: Subscription-based, typically starting from $50-$100 per month per door, plus hardware costs.
Detecting Threats Intrusion Detection and Alarm Systems
Intrusion detection systems (IDS) are designed to detect unauthorized entry or activity within a protected area. When integrated, these systems can trigger video recording, activate access control lockdowns, and alert security personnel via the SMP.
Key Elements of Integrated IDS:
- Sensors: A variety of sensors are used, including door/window contacts, motion detectors (PIR, microwave, dual-tech), glass break detectors, and vibration sensors.
- Alarm Panels: The central hub for the IDS, collecting data from sensors and communicating with the SMP.
- Perimeter Protection: Outdoor sensors (e.g., fence sensors, buried cables, beam detectors) can detect intruders before they even reach the building.
- Environmental Sensors: Integration often extends to smoke, CO, and flood detectors, providing a comprehensive safety net.
Recommended Intrusion Detection Products:
-
Honeywell Vista Series (Panels and Sensors):
- Description: A widely recognized and robust line of wired and wireless intrusion alarm panels and a vast ecosystem of compatible sensors. Known for reliability and extensive features.
- Use Case: Suitable for commercial, industrial, and high-end residential applications requiring a professional-grade intrusion system.
- Pricing: Panels can range from $200-$800, with individual sensors costing $20-$100 each.
-
DSC PowerSeries Neo (Panels and Sensors):
- Description: Offers a hybrid wired/wireless intrusion solution with advanced features, including PowerG wireless technology for extended range and reliability.
- Use Case: Excellent for businesses and larger homes that need a flexible and secure intrusion detection system with advanced encryption.
- Pricing: Similar to Honeywell, panels are in the $200-$700 range, with sensors varying.
-
Bosch Security Systems (Detectors):
- Description: Bosch offers a range of high-performance motion detectors, including those with advanced anti-masking and pet immunity features, designed for professional installations.
- Use Case: Ideal for environments where false alarms need to be minimized and precise detection is critical, such as warehouses, offices, and high-security areas.
- Pricing: Professional-grade motion detectors typically cost $50-$200 each.
Communication and Emergency Response Intercoms and Mass Notification
Effective communication is crucial during a security event. Integrated systems often include intercoms and mass notification capabilities to facilitate rapid response and inform occupants.
Integrated Communication Features:
- Video Intercoms: Allow for visual and audio verification of visitors at entry points, often integrated with access control to grant remote access.
- Mass Notification Systems: Can send alerts via email, SMS, public address systems, and digital signage to inform people about emergencies or instructions.
- Two-Way Audio: Many IP cameras and access control readers now include two-way audio for direct communication with individuals at a specific location.
Recommended Communication Products:
-
Aiphone IX Series (Video Intercoms):
- Description: Aiphone offers robust IP video intercom systems that integrate well with access control and VMS platforms, providing clear audio and video communication.
- Use Case: Ideal for building entrances, gates, and internal communication points in commercial buildings, schools, and multi-tenant residences.
- Pricing: Stations can range from $300 to $1,000+, depending on features.
-
Alertus Technologies (Mass Notification):
- Description: Provides a comprehensive mass notification system that can integrate with existing security infrastructure to deliver alerts across multiple channels (desktop, mobile, PA, digital signage).
- Use Case: Essential for campuses, hospitals, and large corporations needing to disseminate critical information rapidly during emergencies.
- Pricing: Subscription-based, varies significantly based on the number of users and deployment scale.
The Network Infrastructure The Backbone of Integration
All these components rely heavily on a robust and secure network infrastructure. This includes network switches, routers, servers (for VMS, access control databases), and secure cabling (Ethernet, fiber optics).
Key Network Considerations:
- Bandwidth: Sufficient bandwidth is critical, especially for high-resolution IP video streams.
- Redundancy: Redundant network paths and power supplies ensure system uptime.
- Cybersecurity: Network security measures (firewalls, VLANs, encryption) are paramount to protect against cyber threats.
- Storage: Adequate storage solutions (NVRs, SAN, cloud) are needed for video footage and event logs.
Recommended Network Infrastructure Products:
-
Cisco Meraki (Switches and Routers):
- Description: Offers cloud-managed network switches and routers that simplify deployment and management, providing robust performance and security features.
- Use Case: Suitable for organizations looking for easy-to-manage, scalable network infrastructure for their integrated security systems.
- Pricing: Switches can range from a few hundred to several thousand dollars, plus annual licensing fees.
-
Dell EMC PowerEdge Servers:
- Description: Reliable and powerful servers suitable for hosting VMS, SMP, and access control databases, offering scalability and performance.
- Use Case: Essential for larger integrated security deployments requiring dedicated server resources for data processing and storage.
- Pricing: Servers can range from $1,000 to $10,000+, depending on configuration.
Powering It All Power Supplies and Backup Systems
A security system is only as good as its power supply. Integrated systems require reliable power and backup solutions to ensure continuous operation, even during outages.
Power System Components:
- Power over Ethernet (PoE): Simplifies wiring for IP devices by delivering power and data over a single Ethernet cable.
- Uninterruptible Power Supplies (UPS): Provide temporary battery backup power to critical components during short power outages.
- Generators: For extended outages, generators can provide long-term power to the entire security infrastructure.
Recommended Power Products:
-
APC Smart-UPS (UPS Systems):
- Description: A leading brand for UPS systems, offering reliable battery backup and surge protection for network equipment and servers.
- Use Case: Essential for protecting critical security components from power fluctuations and ensuring continuous operation during brief outages.
- Pricing: Varies from $200 for small units to several thousand for large enterprise-grade UPS systems.
-
Altronix (Power Supplies for Access Control/CCTV):
- Description: Specializes in power and transmission solutions for security systems, offering reliable power supplies, often with battery backup capabilities, for access control panels and cameras.
- Use Case: Provides dedicated, stable power for security devices, ensuring they function correctly and reliably.
- Pricing: Power supplies typically range from $50 to $500+, depending on output and features.
The Human Element Security Personnel and Training
While technology is crucial, the human element remains indispensable. Well-trained security personnel are vital for monitoring, responding to alerts, and managing the integrated system effectively.
Importance of Training:
- System Operation: Personnel must be proficient in using the SMP, interpreting alerts, and navigating various system interfaces.
- Emergency Protocols: Clear, well-rehearsed emergency response protocols are essential for effective incident management.
- Cybersecurity Awareness: Training on cybersecurity best practices helps prevent human error from compromising the system.
Putting It All Together The Synergy of Integration
The true power of an integrated security system comes from how these diverse components work together. Imagine a scenario:
A motion sensor (Intrusion Detection) detects unusual activity in a restricted area after hours. The Security Management Platform immediately receives this alert. It then automatically pulls up live video feeds from nearby CCTV cameras, allowing security personnel to visually verify the threat. Simultaneously, the system can trigger an audible alarm, lock down all access points to that specific zone (Access Control), and send a mass notification to on-site security teams and relevant management. All these actions are logged, and detailed reports are generated for post-incident analysis.
This level of coordinated response is impossible with disparate, standalone systems. Integration transforms a collection of devices into a proactive, intelligent security ecosystem.
Choosing the Right Integrated Security System for Your Needs
Selecting the right integrated security system involves careful consideration of several factors:
- Scale and Complexity: How large is your facility? How many entry points, cameras, and sensors do you need?
- Budget: Integrated systems represent a significant investment, so define your budget clearly. Remember to factor in installation, maintenance, and potential software licensing fees.
- Specific Threats: What are the primary security risks you face? (e.g., theft, vandalism, unauthorized access, terrorism, natural disasters).
- Compliance Requirements: Do you need to meet specific industry regulations or certifications?
- Scalability: Can the system grow with your organization's future needs?
- Vendor Reputation and Support: Choose reputable vendors and integrators who offer excellent support and service.
- Open Architecture: Prioritize systems with open architecture for greater flexibility and future integration possibilities.
By understanding each component and how they interoperate, you can make informed decisions to build a robust, efficient, and future-proof integrated security system that truly protects your assets and personnel. It's not just about buying devices; it's about creating a smart, responsive security environment.
:max_bytes(150000):strip_icc()/277019-baked-pork-chops-with-cream-of-mushroom-soup-DDMFS-beauty-4x3-BG-7505-5762b731cf30447d9cbbbbbf387beafa.jpg)